“Recently, my iPhone becomes slow suddenly, can anyone tell me how to know if my iPhone is hacked?” Today, our handsets have become the most important device in our daily lives. We save all of our sensitive, personal, and private information on our iPhones and Android phones. It makes sense that the security of our handsets become a big concern. If something is abnormal with your iPhone, check the signs one by one carefully.

- Part 1: 5 Signs to Tell If Your iPhone Is Hacked
- Part 2: Tips to Avoid iPhone to Be Hacked
- Part 3: FAQs on How to Tell If Your iPhone Is Hacked
Part 1: 5 Signs to Tell If Your iPhone Is Hacked
Sign 1: Unknown App or Pop-ups

When you suspect your iPhone is hacked by someone else, open the Settings app, go to the General entry, and tap iPhone Storage. Here you can get all apps installed on your iPhone. Check them and if you find an unfamiliar app, chances are that your iPhone is hacked.
Sign 2: Battery Consumption

How to check if your iPhone has been hacked? One thing you may notice is the battery draining faster than usual. Of course, a battery wears down over time, but that is over years. If your battery drains quickly, it means that something is going on in the background, such as malicious software.
Sign 3: Performance Issue

An important benefit of iOS devices is the excellent performance. However, if your iPhone is suddenly acting a lot slower, that means the processing power is being used by something else, such as malware. Therefore, that is a sign that tells someone is spying on your iPhone.
Sign 4: Higher Data Usage
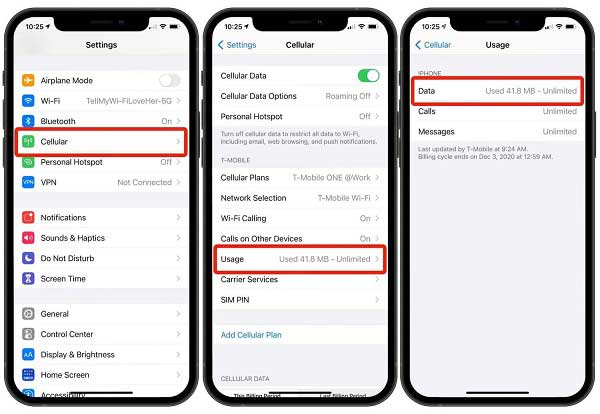
Today, most iPhone users are always online either through a Wi-Fi network or cellular. When your mobile data is draining quicker than ever before, it may tell you someone is accessing your iPhone remotely. You should monitor your data usage in the Settings app regularly.
Sign 5: Strange Calls or SMS

Another important sign that tells your iPhone may be hacked is strange calls or messages. Sometimes, you may receive phone calls or SMS from strangers occasionally. However, if your iPhone sends automated SMS to unknown contacts or you notice random outgoing calls in your call log, you should be cautious.
Part 2: Tips to Avoid iPhone to Be Hacked
How to stop someone from accessing your iPhone remotely is another big problem. In fact, there are somethings you can do to prevent hackers from accessing your iOS device. We list the tips below:
Tip 1: Hide Your GPS Location
Apeaksoft iPhone Location Changer is the easiest way to hide your GPS location on your iPhone. It is well known that Apple does not allow customers to modify their iPhone locations. That gives hackers the ability to track you. Fortunately, the software can help you resolve this problem.
4,000,000+ Downloads
Modify GPS location on iPhone without installing apps.
Hide location for all services and apps on your iPhone.
Support a wide range of iOS devices.
Include lots of bonus features.
How to Hide Your iPhone Location
Step 1Connect your iPhoneRun the iPhone location changer after installing it on your PC. Hook up your iPhone to the same PC with a Lightning cable. Then click the Start button to enter the home interface.
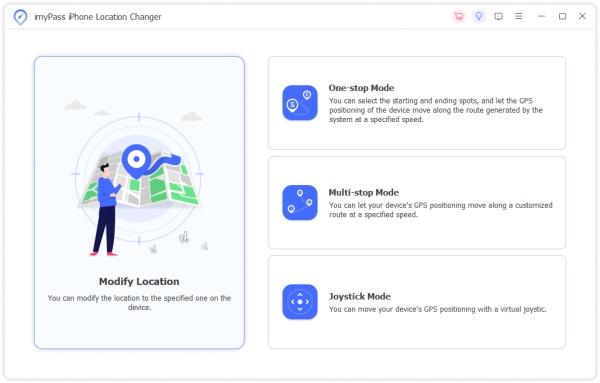 Step 2Modify iPhone location
Step 2Modify iPhone locationTo prevent someone from hacking your iPhone location, click the Modify Location button. Then select a fake location on the map, and click Move to. That’s All.
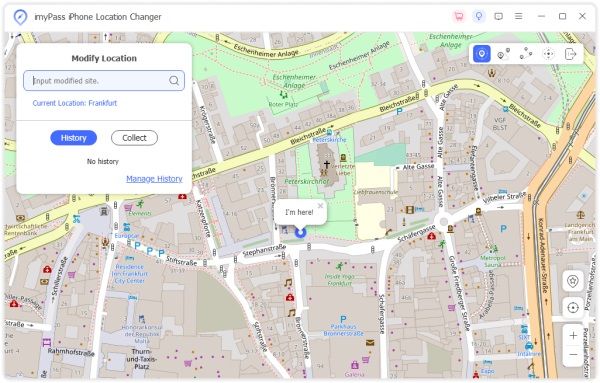
Note: If you have an accurate address, type in the box on the popup dialog, and click Modify to change your iPhone location. Besides, the software enables you to make virtual routines with one-stop, multiple stops, or using Joystick Mode.
Tip 2: Keep Software Update

Apple releases updates frequently in order to fix bugs and flaws that hackers cloud use to access iPhones. Therefore, you should always update your iOS device to the latest software. The easiest way is to toggle on the Automatic Updates option in the Software Update screen in your Settings app.
Tip 3: Manage App Permissions

When you install an app, it may ask for some permissions, like accessing your photos, camera, and more. That gives hackers the chance to access your iPhone memory. You’d better refuse the unnecessary permissions. Go to the Settings app, tap Privacy, and choose permission. Then you will see which apps get this permission and disable it.
Tip 4: Avoid Public Charging

The public chargers controlled by hackers are called Juice Jacking. It means hackers load malware or steal data from phones through a USB cable in public charger stations. This act can happen wherever public charging stations are located, such as airports, hotels, bus stations, etc. Therefore, you’d better charge your iPhone at home and avoid your iPhone being hacked.
Part 3: FAQs on How to Tell If Your iPhone Is Hacked
Question 1. Can you get rid of a hacker in your iPhone?
You can install an antivirus app on your iPhone or do a factory reset to get rid of a hacker. However, that does not guarantee the removal of malware that the hacker has installed on your iPhone.
Question 2. What you can do when your iPhone is hacked?
Firstly, back up important data and files on your iPhone to another device. Then delete suspicious apps from your iPhone, and install antivirus software. Finally, perform a factory reset on your device.
Question 3. Can hackers see your iPhone screen?
Yes. Malware is a kind of software that hackers can use to see what you do on your iPhone screen and control your device. Due to Apple’s security rules, the malware won’t come from App Store. However, it may come from your email, messages, or websites.
Conclusion
Now, you should understand how to tell if someone is hacking your iPhone remotely, stealing your information, and spying on your activities. If you suspect your iPhone is hacked, you can check the signs on your handset. To prevent hackers from accessing your device, Apeaksoft iPhone Location Changer is a great tool. More questions about this topic? Please feel free to leave a message below this post and we will reply to it as soon as possible.




